Top 7 Best Practices to Outsource Cybersecurity Successfully
Discover the top 7 strategies for successful cybersecurity outsourcing and multiple pieces of advice in a comprehensive guide by Fively cybersecurity specialists.
In today's digital era, protecting your software and digital assets is not just a technical necessity but a strategic imperative. According to the latest info by Cybersecurity Ventures, damages from cybercrime are expected to exceed $10.5 trillion globally by 2025.
As cyber threats grow more sophisticated and pervasive, businesses of all sizes find themselves in a relentless battle to protect their digital assets and maintain customer trust. Cybersecurity outsourcing emerges as a strategic solution, offering access to top-tier expertise and cutting-edge technology.
Yet, the path to successful outsourcing is fraught with considerations, from selecting the right partner to ensuring seamless integration with existing operations. Today Fively as a leader in custom software solutions will help you navigate this complex landscape and outsource your security needs successfully. Are you ready? Here we go!
What are the Benefits of Outsourcing Cybersecurity?
First, let’s see why companies decide to outsource cybersecurity: what benefits can it give them? Outsourcing extends beyond merely delegating tasks; it's about enhancing your cyber defense with a dedicated, specialized force. Below, we explore the multifaceted benefits that make outsourcing cybersecurity not just an option but a strategic necessity for modern enterprises.
Continuous Support
Outsourced cybersecurity teams offer continuous monitoring and immediate response capabilities, ensuring that your network and systems are watched over at all times. This relentless vigilance helps to swiftly identify and mitigate potential threats, minimizing downtime and safeguarding business operations around the clock.
Lower Costs
By outsourcing, companies can avoid the significant expenses associated with recruiting, training, and retaining an in-house cybersecurity team, including the costs of advanced tools and technologies. This model allows for predictable budgeting with flexible service packages tailored to specific security needs and financial constraints.
Access to Expertise
Outsourcing partners bring a depth of knowledge gained from wide-ranging experiences across industries, offering insights and solutions that might not be available in-house. This expertise is continually updated, ensuring your protection measures evolve to counter new and emerging threats effectively.
Early Warnings on Emerging Threats
Specialized cybersecurity firms have the networks and tools to detect emerging threats early, often before they become public knowledge. This proactive stance allows your organization to prepare and defend against new types of attacks, keeping you one step ahead of cybercriminals.
Independent Assessment
An external cybersecurity provider can objectively assess your security posture without the bias that might affect internal teams, offering a fresh perspective on vulnerabilities and risk management strategies. This independence is crucial for developing a comprehensive and effective cybersecurity framework that truly protects your assets.
Reliability and Sustainability
Outsourced cybersecurity services are built on a foundation of reliability, with teams dedicated to maintaining up-to-date defenses against cyber threats. This approach ensures the sustainability of your security efforts, adapting over time to protect against the ever-evolving landscape of cyber threats.
Scalability
The flexibility of outsourced cybersecurity services means they can be quickly adjusted to accommodate your organization's growth, seasonal fluctuations, or specific project needs. This scalability ensures that your digital protection posture is always aligned with your current operational requirements, without the need for constant internal restructuring.
In-depth Knowledge of Regulatory Requirements
With regulations and compliance standards constantly evolving, outsourced cybersecurity providers specialize in staying informed about these changes, ensuring your organization adheres to the latest legal and industry-specific security requirements. This knowledge is vital for maintaining compliance and avoiding potential legal and financial penalties.
Early Adoption of New Technologies
Cybersecurity firms invest heavily in the latest security technologies and practices, giving their clients access to advanced tools and methodologies without the need for significant internal investment. This early adoption can provide a competitive edge in cybersecurity, offering superior protection against sophisticated threats.
By tapping into the wealth of benefits that outsourcing offers, businesses can not only fortify their defenses against cyber threats but also align their cybersecurity strategy more closely with their operational and financial goals, ensuring a secure, resilient future.
Drawbacks of Outsourcing Cybersecurity
While outsourcing offers a plethora of benefits, from access to expertise to cost savings, it's not without its challenges. Understanding these potential drawbacks is crucial for organizations to make informed decisions and implement strategies that mitigate risks.
Below, our experts delve into the key concerns that can arise when outsourcing cybersecurity, offering insights into how each can impact your organization and how to address them effectively.
Less Control
Outsourcing cybersecurity operations often means relinquishing direct control over how specific security tasks and policies are executed. This can lead to a sense of disconnect between an organization’s internal security goals and the outsourced provider’s methods.
To mitigate this, it’s essential to establish clear communication channels, set detailed expectations, and regularly review the service provider’s performance against agreed benchmarks.
Lack of Communication
Effective communication is the backbone of any successful outsourcing relationship, yet differences in time zones, languages, and cultures can pose significant barriers. Misunderstandings or delays in communication can hinder timely responses to security incidents or complicate the execution of security strategies.
Overcoming these challenges requires selecting a provider with a strong track record of effective communication and ensuring regular, structured updates are part of the service agreement.
Reliability and Quality Concerns
Entrusting your cybersecurity to an external party introduces concerns about the reliability and quality of the services provided. There’s a risk that the outsourced partner may not meet the expected standards, potentially leaving vulnerabilities unaddressed.
To counteract this, thorough due diligence during the selection process, including reviews of the provider’s track record, client testimonials, and industry certifications, is crucial.
Biased Decision-Making
Outsourced cybersecurity providers may have preferences or biases toward certain technologies or strategies based on their expertise, partnerships, or business models, which might not always align with your organization’s best interests. This can lead to recommendations that are more beneficial to the provider than to the client.
Ensuring transparency in decision-making, and maintaining an active role in strategic discussions, can help mitigate the risk of biased recommendations.
Recognizing these drawbacks is not a deterrent to cybersecurity outsourcing but rather a guide to doing so thoughtfully and strategically. By understanding potential pitfalls and implementing measures to address them, organizations can enjoy the benefits of outsourcing while minimizing the risks, ensuring a robust cybersecurity posture that aligns with their business objectives.
What to Outsource vs. What to Keep In-House in Cybersecurity?
Now, we finally come to the most important part of this guide: how to decide which parts of your data, services, and processes you can protect with the help of outsourcing?
The decision to outsource certain security functions while retaining others in-house is pivotal, influencing not just security posture but also operational agility and business focus. This balance requires a strategic approach, considering both the organization's specific security needs and its capacity to manage them. Below, we outline key cybersecurity functions that are commonly outsourced, alongside those that typically benefit from an in-house approach, helping you navigate this critical decision-making process.
What You Can Outsource:
1. Custom Software Solutions Security
Outsourcing the development and securing of custom software solutions enables access to specialized skills and technologies tailored to your specific business requirements. This approach not only accelerates the development cycle but also ensures that the software is highly secure, and integrated seamlessly with existing systems.
Partnering with experienced developers for custom cybersecurity solutions allows businesses to focus on core operations while benefiting from innovative, bespoke software that drives growth and efficiency:
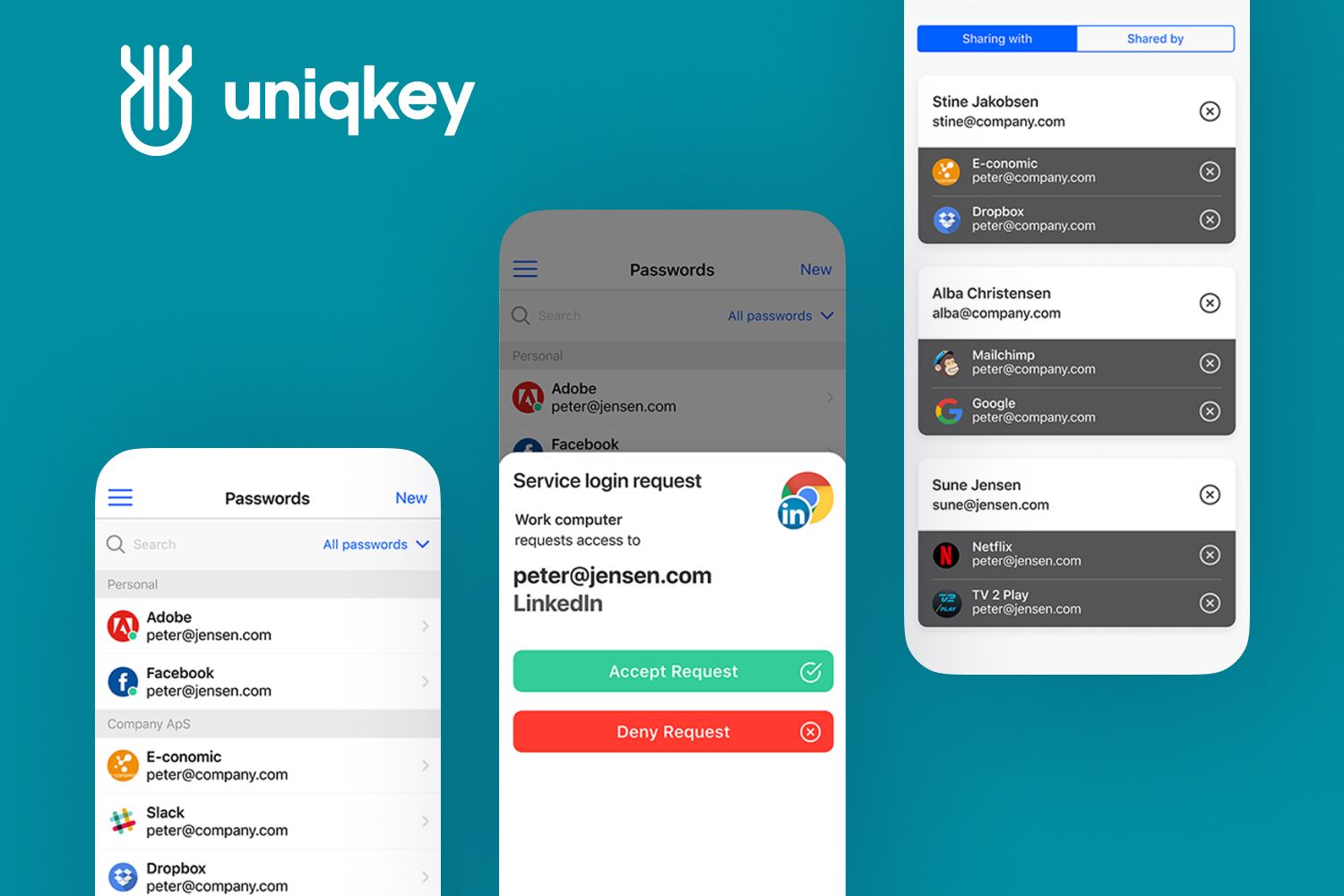
Fively develop custom software solutions to protect data, provide secure assets, prevent fraud, and mitigare risks
We emplement various security software solutions including special browser extensions to keed data secure;
Our experienced software developers can strengthen or improve the security of your legacy software and computer operation systems.
2. Cybersecurity Monitoring and Incident Response
Outsourcing continuous monitoring and incident response leverages external expertise to detect and respond to threats swiftly. This ensures round-the-clock vigilance without the need to develop and maintain a 24/7 in-house team.
3. Vulnerability Assessments and Penetration Testing
Third-party providers bring fresh perspectives and up-to-date methodologies to identify vulnerabilities, making it a smart function to outsource for unbiased, comprehensive assessments.
4. Compliance Management
Staying abreast of regulatory requirements and ensuring compliance can be complex and resource-intensive. Outsourced experts in compliance can navigate these waters efficiently, reducing the risk of non-compliance penalties.
5. Security Awareness Training
Cybersecurity education providers specialize in creating engaging training content and platforms, helping to cultivate a security-aware culture more effectively than in-house resources might.
5. Threat Intelligence and Analysis
Gaining access to global threat intelligence and analysis through outsourcing can enhance your security strategy with insights and trends beyond the reach of most in-house teams.

What We Recommend to Keep In-House:
1. Cybersecurity Strategy and Governance
Strategic planning, including setting overarching security policies and governance, should remain under the direct control of internal leadership to ensure alignment with business objectives.
2. Core Business Application Security
The security of applications critical to your business operations might be best managed in-house, given the internal team's intimate understanding of the business processes and needs.
3. Data Privacy Management
Handling sensitive customer and business data, especially in industries with stringent privacy regulations, often requires the nuanced understanding and control an in-house team provides.
4. Insider Threat Management
Managing and monitoring insider threats involves sensitive information and access that may be more securely controlled by a trusted internal team.
This strategic blend we propose can ensure that while operational efficiencies and advanced capabilities are gained through outsourcing, critical oversight, and core competencies remain firmly within the grasp of the organization, safeguarding its digital horizon.
Top 7 Best Practices to Outsource Cybersecurity
Now, that you already know what security parts you can outsource, it’s time to get down to the best practices that will help you to do it right:
1. Choosing the Type of Cybersecurity Services You Need
Cybersecurity encompasses a broad spectrum of areas, including network security, application security, information security, operational security, business continuity, disaster recovery, and end-user education. Identifying the specific areas your organization needs to focus on is the first step toward building a robust digital protection posture. Each category addresses different vulnerabilities and threats, requiring tailored strategies to protect your digital landscape effectively.
For example, we at Fively provide the following custom cyber security solutions and services:
- Identity and access management (IAM) apps
We build digital security solutions that allow you to manage user authentication and give access to authorized users. It is simple and effective.
- Role-based access control (RBAC) systems
Our experience in software development and cyber security enables us to build systems that provide access to certain data based on job roles and devices.
- Remote monitoring and management software
We use our expertise in software development, cyber security, and monitoring technology to implement effective solutions for remote management.
- Fraud detection and prevention solutions
We build applications for transaction monitoring and fraud prevention based on the latest research and development in cyber security technology.
2. Setting a Budget for Cybersecurity
Allocating an appropriate budget for cybersecurity is essential. A comprehensive cost/benefit analysis will help you understand the investment needed to safeguard your organization. In most cases, the security budget ranges from 5% to 20% of an organization’s IT spending, underscoring the financial commitment required to mitigate the risk of data breaches and cyberattacks.
3. Check the Portfolio of Your Cybersecurity Provider
Partnering with a cybersecurity provider with a proven track record and solid reputation is crucial. Research their past projects, client testimonials, and any industry accolades to gauge their expertise and reliability. A provider with extensive experience in your specific sector or with the types of cybersecurity challenges you face can offer invaluable insights and solutions.
4. Define Your Team’s Skillset
Understand the cybersecurity skills and capabilities of your in-house team. This will help you identify the areas where outsourcing can provide the most value, ensuring a complementary blend of internal and external cybersecurity efforts. Knowing your team's strengths and weaknesses allows for a more strategic outsourcing decision.
5. Adopt a Forward-Thinking Approach
Cybersecurity is not static; it evolves rapidly as new threats emerge and technologies advance. Choose a cybersecurity provider that demonstrates a forward-thinking approach, investing in emerging technologies and staying ahead of the latest cybersecurity trends and threats. This ensures your security measures remain effective over time.
6. Ensure Clear Communication and Collaboration
Effective communication between your organization and the cybersecurity provider is vital for the success of the outsourcing partnership. Establish clear channels and protocols for reporting, updates, and incident response. Regular meetings and reviews can help align strategies and ensure both parties are working towards the same goals.
7. Prioritize Compliance and Regulatory Requirements
Ensure your cybersecurity provider is well-versed in the compliance and regulatory requirements relevant to your industry. Outsourcing should not only aim to protect against cyber threats but also to maintain compliance with laws and regulations, avoiding potential legal and financial penalties.
By adhering to these best practices, organizations can navigate the complexities of cybersecurity outsourcing with confidence. The goal is to create a partnership that extends beyond mere service provision, fostering a collaborative effort that enhances your cybersecurity posture while aligning with your business objectives.
Mastering the Art of Cybersecurity Outsourcing with Fively
Our exploration into the best practices for outsourcing cybersecurity underscores a holistic approach, emphasizing the importance of clarity in requirements, budgetary foresight, and the selection of a reputable provider. By defining your team's skillset, adopting a forward-thinking approach, ensuring seamless communication, and prioritizing compliance, organizations can forge partnerships that not only bolster their cybersecurity defenses but also align with their broader business goals.
With the right partner, proactive planning, and adherence to the best practices outlined, your journey toward outsourced cyber security solutions can lead to a more secure, resilient, and confident future in the digital realm.
Let Fively be your guide in this critical endeavor, offering the custom software applications and solutions you need to navigate the cybersecurity landscape successfully. Don’t hesitate to contact us if you need to build any cybersecurity solutions, and together, we can create a safer digital world for your business and your customers. Let’s fly!

Need Help With A Project?
Drop us a line, let’s arrange a discussion