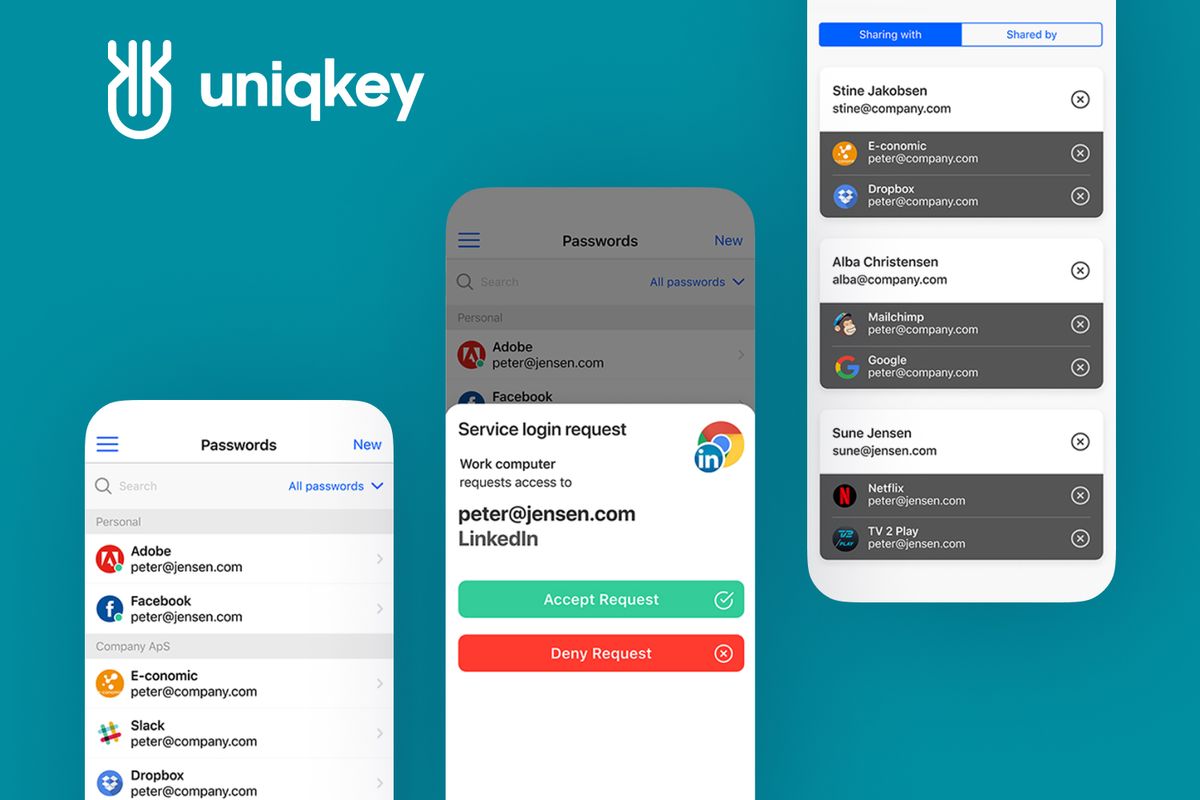
About Uniqkey
Uniqkey is a cybersecurity company headquartered in Denmark. The company is engaged in providing identity and access management automation services based on cloud technologies.
Today, Uniqkey's IAM solutions are very popular with small and medium-sized businesses, both at home and abroad.
Country
Denmark
industry
Cybersecurity
timeline
27 months
team
1-5 developers
Tech stack
6
layers of encryption
4x
faster log in process
3,000+
users in Chrome Web Store only
Fively Reviews
Powered by
THE PROJECT
Mobile App & Web Dev for Cybersecurity Company
The review
"They have their heads in the game, and they care about the project rather than finishing it as quickly as possible."
Aug 20, 2019
Feedback summary
Fively’s team mentality and skills are very impressive. They work hard to design effective software architecture and find ways to improve on the client's ideas. In regard to project management, they were clear with deadlines and any potential changes.
the project
Mobile App Development
$50,000 to $199,999
Dec. 2018 - Ongoing
PROJECT summary
Fively provides external developers for a cybersecurity company. They do iOS and Android app development, as well as web app development with React and Angular. The team also executes UX design.
THE REVIEWER
CTO, Uniqkey
Kasper Fogh
IT Services
Copenhagen, Denmark
11-50 Employees
Phone Interview
Verified
Need Help With a Project?
Drop us a line, let’s arrange a discussion
What Is IAM Automation?
Identity and access management (or IAM) system is a secure password management software that is used by many companies to create strong passwords, safely store and manage them without a hitch.
As a rule, such IAM automation tools are used to streamline business processes associated with routine access controls procedures and time-consuming distribution of access privileges in order to completely eliminate any possibility of some human error.
IAM software is the pillar of cybersecurity for many modern-day companies that use cloud-based applications. In cases when an employee deals with a dozen of web services on a daily basis, the temptation is extremely strong to utilize simple passwords that are easy to remember or even reuse some oldy-moldy password that is used for a bunch of other accounts.
Storing passwords in an inappropriate place, such as a document on a computer's desktop, can pose a dire threat to private data as well. Thus, even the strongest password could be stolen, and all best endeavors would go down the drain.
Of course, such negligence may create a maze of vulnerabilities that hackers will certainly exploit to gain access to internal data. Fortunately, there are some IAM software solutions that could save the day.
The Challenges of IAM Automation Tools Development
We started working with Uniqkey to build an unparalleled and feature-rich B2B password manager that could become a real breakthrough in the cybersecurity industry.
The main reason Uniqkey's managers made up their minds to team up with Fively was that they couldn't find developers who could surpass our level of expertise and professional attributes. Having considered these criteria to be vital when it comes to developing cybersecurity products, the owners of Uniqkey decided that our reliable team of software engineers would be the best choice available.
The major challenge was to develop a really smart identity and access management tool that can securely store credentials and use them for login to any web platform and service. We sought to build a robotic process automation identity access management software that would be better than just an ordinary IAM system and provide the end-user with a comprehensive set of handy tools for secure storage and convenient use of passwords.
Since it is a B2B product, our task was to think over how to make this particular software solution friendly for corporate use and eminently suitable for any business, regardless of the industry and other factors.
Did we manage to do it? - We did it like a charm
How Fively Helped Uniqkey Create an Innovative IAM Solution
Automation in identity and access management is a crucial component that can accelerate the digital transformation process and help businesses manage access to their accounts even more effectively and timely.
What is more important, Uniqkey does not have to worry about data leaks and other threats to their cybersecurity if they have a reliable and user-friendly IAM solution that allows employees to have easy access to all the cloud services and web platforms they need to deal with.
Just such a product we have created, working meticulously hand in hand with Uniqkey. To put it in a nutshell, months of our collaborative efforts have resulted in the cutting-edge robotic process automation identity access management software, which is available for use on a wide range of devices, including smartphones and desktop computers.
Another big draw of this all-in-one product is that it supports multi factor authentication, which greatly reduces the chances of passwords getting into the hands of the wrong people. We've also implemented a password analysis feature that comes in handy in cases when user passwords turn out to be too weak or pretty reused.
Taking all these factors into consideration, it's no surprise that the project broke into the big time fairly soon. Today, Uniqkey is recognized by a number of top-tier companies all around the globe. The startup has won some prestigious awards in the field of innovation at home as well.
Do not forget that for the entire time of its operation, this password management software has made a significant contribution to the identity automation industry and saved thousands of user accounts from cyber intruders.
The Result
Summing up the results of our cooperation, our engineers have done a brilliant job and developed a truly advanced password management software, which right now stands sentinel over dozens and dozens of businesses, securely protecting their accounts on the Internet from swarming cyber threats.
Working hand in hand with Uniqkey, we have created an identity management system that is not unreasonably priced and can suit the budgets of small companies and even sole entrepreneurs. At the same time, businesses need this very product badly, as they're beginning to take their cybersecurity more seriously. In view of this, reliable software for identity and access management automation, namely the solution developed by our engineers, is gradually becoming the core element upon which the security of entire companies in and out of Denmark is hinged.
The passwordless authentication solution that was developed in collaboration with Uniqkey is a powerful tool for companies of any size, which will save some precious time for your employees without compromising the security of your business.
In general, I'm really impressed by the developers and the way they carry out work.
Kasper Fogh
Chief Technology Officer, Uniqkey
Technology Stack for IAM Development
For Uniqkey, our IAM automation developers have built a whole set of solutions that includes mobile applications for iOS and Android, extensions for popular browsers, and a web app. The following technologies were used:
- Angular
- React